Learn how to ensure app security and testing with best practices, tools, development process, and strategies to protect mobile and web applications.
How Do I Ensure App Security and Testing?
Mobile and web applications handle sensitive user data, financial transactions, and critical business processes. As digital platforms grow more complex, developers and businesses often ask: how do I ensure app security and testing? Ensuring strong application security and thorough testing is essential to protect user information, prevent cyber threats, and maintain trust with customers.
Modern applications face multiple security challenges, including data breaches, unauthorized access, malware attacks, and vulnerabilities within third-party libraries. Without proper security measures and testing protocols, even small vulnerabilities can lead to serious consequences such as financial losses, regulatory penalties, and damage to brand reputation.
App security and testing involve implementing secure coding practices, encrypting sensitive data, performing vulnerability scans, and conducting continuous testing throughout the development lifecycle. Security must be integrated from the earliest design stages rather than added as an afterthought.
A well-designed security strategy includes authentication systems, secure APIs, encryption protocols, penetration testing, and regular updates to address emerging threats. In addition, quality assurance testing ensures that applications function properly across devices, operating systems, and network environments.
In this guide, we will explore how to ensure app security and testing, including the importance of secure development, types of security solutions, testing processes, technology stacks, cost factors, and emerging trends in application security.
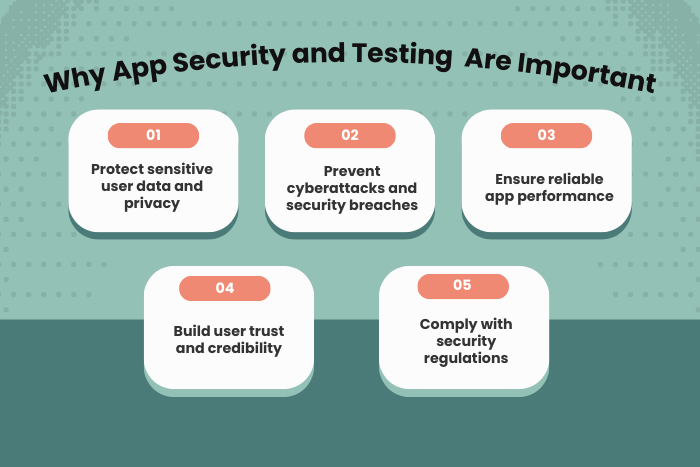
Why App Security and Testing Are Important
Security and testing are critical components of modern application development. Businesses must protect sensitive data while delivering reliable applications that provide seamless user experiences.
Here are several reasons why app security and testing are essential:
Protection of Sensitive User Data
Applications often store personal information, payment details, and login credentials that must be protected.Prevention of Cyberattacks
Security testing helps identify vulnerabilities before hackers exploit them.Compliance with Regulations
Businesses must follow security standards such as GDPR, HIPAA, and PCI DSS.Improved Application Performance
Testing ensures that apps perform efficiently across different devices and environments.Enhanced Customer Trust
Secure applications build confidence among users and encourage long-term engagement.Reduced Risk of Financial Loss
Security breaches can result in costly damages and legal consequences.
Implementing robust security measures and continuous testing ensures that applications remain reliable and protected against threats.
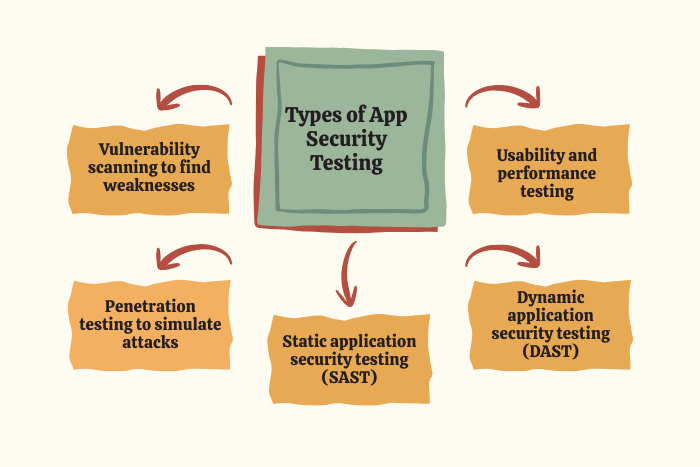
Types of Solutions
Different types of security and testing solutions are used to protect applications and ensure high-quality performance.
Authentication and Authorization Security
Implement secure login systems, multi-factor authentication, and role-based access control.Data Encryption Solutions
Protect sensitive information using encryption techniques during storage and transmission.Network Security Testing
Ensure secure communication channels using HTTPS, secure APIs, and certificate pinning.Vulnerability Scanning
Identify weaknesses in application code, libraries, and configurations.Penetration Testing
Simulate cyberattacks to test the strength of security defenses.Static Application Security Testing (SAST)
Analyze source code to detect vulnerabilities during development.Dynamic Application Security Testing (DAST)
Test running applications to identify security weaknesses.Usability and Functional Testing
Verify that the application functions correctly across different environments.
Combining multiple testing techniques helps ensure comprehensive application security.
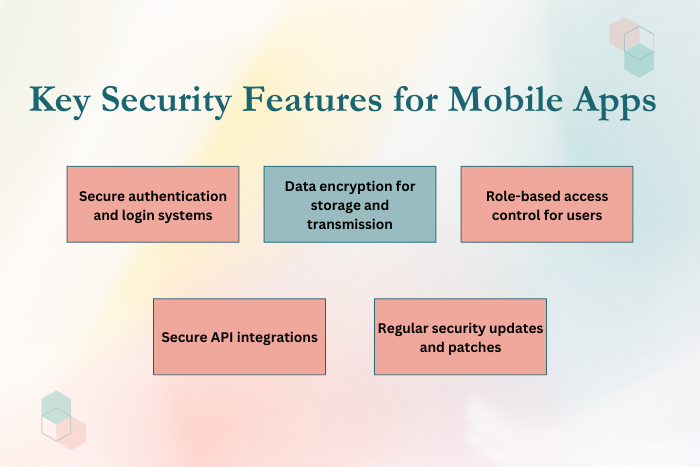
Key Features of Secure App Development and Testing
Secure application development involves several important features that protect systems from potential threats.
Key features include:
Secure authentication and user identity management
Multi-factor authentication for additional security
Strong encryption protocols for data protection
Secure API integration and access management
Input validation to prevent injection attacks
Role-based access control for sensitive operations
Continuous vulnerability monitoring and scanning
Automated testing and security audits
Code reviews and static analysis tools
Secure data storage practices
Runtime application self-protection (RASP)
Regular updates and security patches
These features ensure that applications maintain strong security standards while providing reliable functionality.
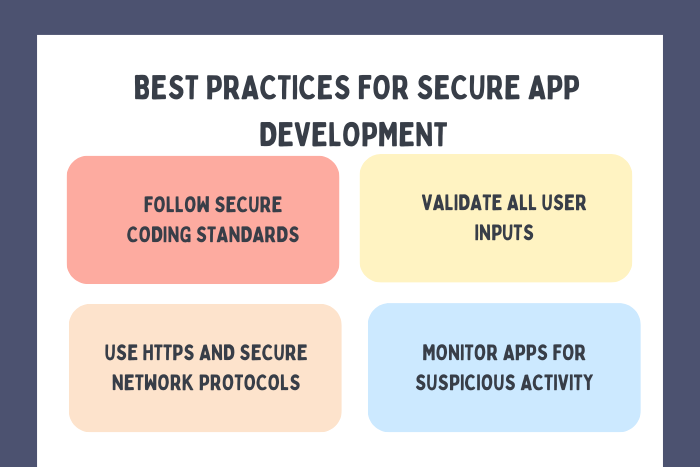
Development Process
Implementing security and testing requires a structured development workflow that integrates security practices at every stage.
Security Planning and Risk Assessment
Identify potential security threats and define protection strategies.Secure Architecture Design
Design application architecture with built-in security controls and data protection mechanisms.Secure Coding Practices
Follow coding standards that minimize vulnerabilities and prevent common attacks.Integration of Security Tools
Implement encryption libraries, authentication systems, and security monitoring tools.Static and Dynamic Security Testing
Conduct code analysis and runtime testing to detect vulnerabilities.Penetration Testing
Simulate real-world cyberattacks to evaluate security defenses.Performance and Compatibility Testing
Ensure the app functions correctly across different devices and operating systems.Deployment and Security Monitoring
Launch the application and monitor security events in real time.Continuous Updates and Patch Management
Regularly update the application to address new vulnerabilities.
Following this process ensures strong security and reliable application performance.
Technology Stack for App Security and Testing
A modern security technology stack includes tools and frameworks designed to protect applications from cyber threats.
Security Frameworks: OWASP Mobile Security, Secure Coding Guidelines
Authentication Technologies: OAuth 2.0, JWT, Multi-Factor Authentication
Encryption Technologies: SSL/TLS, AES encryption, secure key management
Testing Tools: Selenium, Appium, TestGrid, Burp Suite
Security Testing Tools: SAST, DAST, vulnerability scanners
Monitoring Tools: Splunk, Datadog, New Relic
Cloud Security Platforms: AWS Security Hub, Azure Security Center
DevOps Tools: Docker, Kubernetes, CI/CD pipelines
Using the right technology stack helps maintain secure and scalable applications.
Cost Factors in App Security and Testing
The cost of implementing security and testing depends on multiple factors related to application complexity and required protection levels.
Important cost factors include:
Complexity of the application architecture
Number of security features implemented
Testing tools and security software licenses
Third-party security integrations
Penetration testing and vulnerability assessments
Compliance with regulatory standards
Development team expertise and size
Cloud infrastructure and monitoring tools
Ongoing maintenance and security updates
Although security implementation adds to development costs, it significantly reduces the risk of costly security breaches.
Latest Trends in App Security and Testing
Application security is evolving rapidly as new threats and technologies emerge.
Key trends include:
AI-powered threat detection systems
Zero-trust security architectures
Automated vulnerability scanning tools
Biometric authentication systems
Runtime application self-protection (RASP)
DevSecOps integration within development pipelines
Cloud-native security solutions
Advanced API security frameworks
These technologies are helping organizations strengthen their security strategies while maintaining high performance.
Why Choose Us for App Security and Testing?
Choosing the right development partner is essential for building secure and reliable applications. Our team specializes in implementing advanced security frameworks and comprehensive testing strategies.
Here’s why businesses trust our services:
Security-First Development Approach
We integrate security into every stage of the development lifecycle.Advanced Testing Expertise
Our team performs automated testing, penetration testing, and vulnerability assessments.Compliance with Industry Standards
We follow global security standards such as OWASP guidelines.Scalable Security Architecture
Our solutions protect applications as user bases and data volumes grow.Cross-Platform Testing
Applications are tested across Android, iOS, and web environments.Real-Time Monitoring and Threat Detection
Continuous monitoring helps detect and respond to potential threats.Agile Development and Security Integration
Fast development cycles with continuous security improvements.Long-Term Maintenance and Security Updates
Ongoing support ensures applications remain protected against emerging threats.
Ready to secure and test your application effectively?
Let our experts implement advanced security and testing strategies for your app.
Contact us today for a free consultation and security assessment.
Key Points :
- App security protects sensitive user data and prevents cyber threats such as data breaches and unauthorized access.
- Security measures include encryption, secure authentication, and role-based access control.
- Security testing methods include vulnerability scanning, penetration testing, SAST, and DAST.
- Regular testing helps identify bugs, security flaws, and performance issues before app deployment.
- Modern tools like OWASP security frameworks and automated testing platforms improve app security.
- Continuous monitoring, updates, and patch management are essential for maintaining long-term app security.
FAQ's
Implement secure coding practices, integrate encryption, perform vulnerability scanning, and conduct continuous testing throughout the development lifecycle.
Mobile app security testing identifies vulnerabilities and ensures that applications protect sensitive user data and system resources.
Common vulnerabilities include insecure data storage, weak authentication, insecure APIs, and insufficient encryption.
Popular tools include SAST tools, DAST scanners, penetration testing tools, and automated testing frameworks.
Security testing should be performed continuously during development and regularly after deployment.
Automated tools detect many vulnerabilities, but manual testing and penetration testing are also necessary.
Encryption protects sensitive data during transmission and storage, preventing unauthorized access.