Discover app development best practices for security, including encryption, secure APIs, authentication, testing, and compliance strategies.
What Are the App Development Best Practices for Security?
If you’re asking, “What are the app development best practices for security?”, you’re already taking the most important step toward building a safe, reliable, and trustworthy application. In today’s digital landscape, mobile and web applications handle sensitive data such as personal information, payment credentials, business records, and authentication tokens. Without robust security practices, applications are vulnerable to cyberattacks, data breaches, API exploitation, and compliance violations.
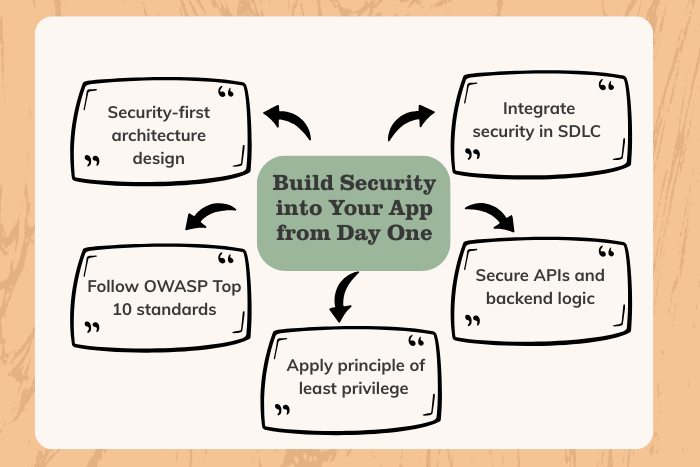
Secure app development is not just about adding encryption at the end of the project. It requires a proactive, security-first approach embedded throughout the entire software development lifecycle (SDLC). From secure architecture design and authentication mechanisms to encrypted data storage, secure network communication, and continuous monitoring, every layer must be protected.
This comprehensive guide explains app development best practices for security, covering architecture design, authentication, data protection, testing strategies, compliance requirements, and modern DevSecOps approaches to help you build secure, scalable, and compliant applications.
Why App Security Best Practices Are Important
Application security directly impacts business credibility, legal compliance, and customer trust. Ignoring security best practices can lead to financial losses, reputational damage, and regulatory penalties.
Here’s why implementing secure app development practices is critical:
Protects sensitive user data and personally identifiable information (PII)
Prevents unauthorized access and account takeovers
Reduces risk of API abuse and data breaches
Ensures compliance with GDPR, HIPAA, PCI-DSS, and other standards
Safeguards intellectual property and business logic
Improves customer confidence and brand reputation
Minimizes costly post-launch security fixes
Modern applications face threats such as SQL injection, cross-site scripting (XSS), insecure direct object references, broken authentication, and supply chain vulnerabilities. Integrating security best practices early significantly reduces risk and long-term costs.
Types of App Security Solutions
To answer “What are the app development best practices for security?”, it’s essential to understand the different layers of protection involved:
Secure Architecture & Design
Security-by-design principles, threat modeling, and least privilege architecture.Authentication & Authorization Security
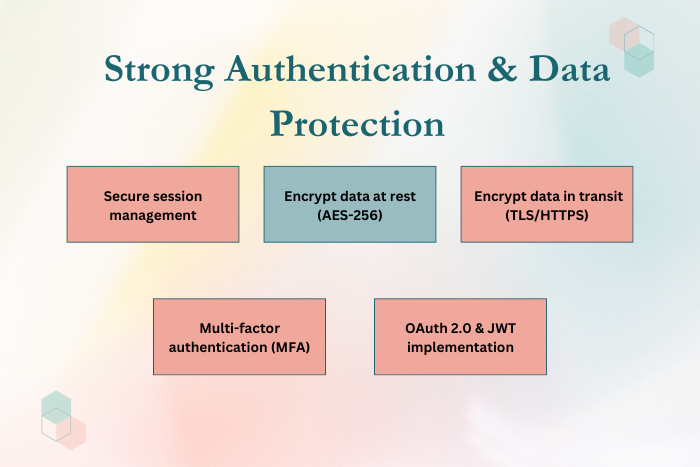
Multi-factor authentication (MFA), role-based access control (RBAC), and secure session management.Data Protection & Encryption
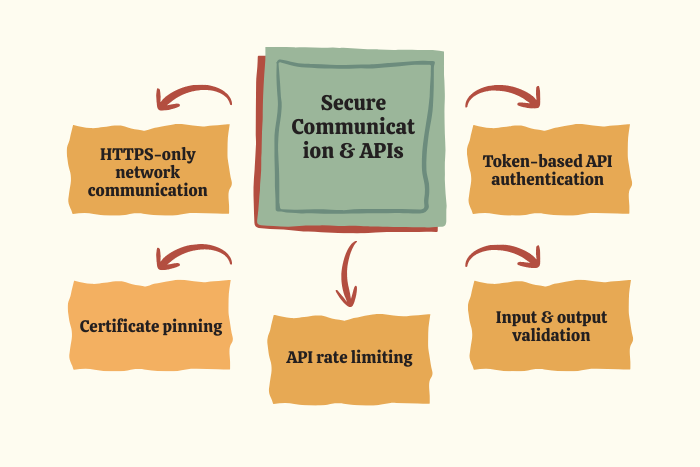
Encryption in transit (TLS/HTTPS) and encryption at rest for databases and storage.Secure API Development
API authentication tokens, rate limiting, input validation, and monitoring.Network Communication Security
Certificate pinning, secure protocols, and firewall configuration.Code & Dependency Security
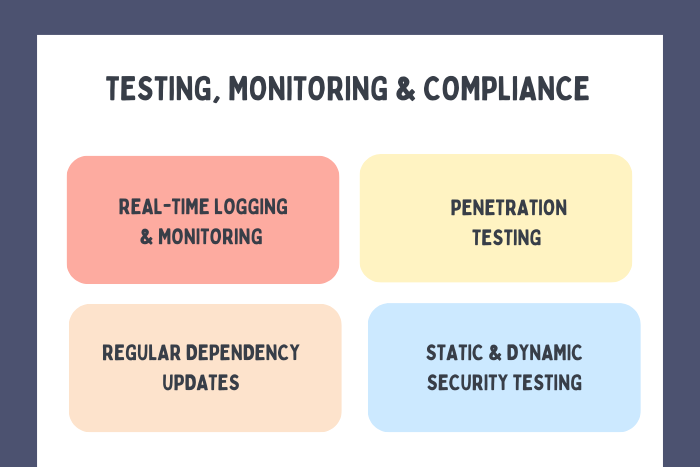
Static code analysis, dependency scanning, and patch management.Post-Deployment Monitoring & Incident Response
Logging, anomaly detection, vulnerability scanning, and rapid patching.
A comprehensive approach ensures protection across all layers of the application stack.
Key Features of Secure App Development
A secure application must include these essential features:
End-to-end encryption (TLS 1.2+)
Secure authentication (OAuth 2.0, JWT, MFA)
Role-based and least-privilege access controls
Secure API gateways with rate limiting
Data encryption at rest
Secure storage mechanisms (Keychain, Keystore)
Regular dependency updates and patch management
Secure coding standards aligned with OWASP Top 10
Real-time logging and monitoring
Automated security testing in CI/CD pipelines
Security must be measurable, auditable, and continuously monitored.
Development Process
Embedding security into the development lifecycle ensures long-term resilience.
Threat Modeling & Risk Assessment
Identify potential vulnerabilities, attack vectors, and data sensitivity.Secure Architecture Design
Implement least privilege access, secure APIs, and encrypted communication channels.Secure Coding Implementation
Follow industry standards to prevent injection attacks, broken authentication, and insecure deserialization.Authentication & Authorization Setup
Implement MFA, token-based authentication, and secure session handling.Data Protection & Encryption Configuration
Encrypt data in transit (HTTPS/TLS) and at rest in databases.Security Testing & Code Review
Perform static analysis, dynamic testing, penetration testing, and vulnerability scans.Dependency & Supply Chain Management
Audit third-party libraries and keep frameworks updated.Deployment with DevSecOps Integration
Automate security checks within CI/CD pipelines.Monitoring & Incident Response Planning
Establish logging, monitoring dashboards, and rapid patch procedures.
This structured process reduces vulnerabilities before and after launch.
Technology Stack for Secure App Development
Choosing secure and scalable technologies strengthens application defense mechanisms.
Frontend: React, Angular, Swift, Kotlin
Backend: Node.js, Django, .NET Core, Spring Boot
Authentication: OAuth 2.0, OpenID Connect, JWT, MFA
Encryption: TLS/HTTPS, AES-256
API Security: API gateways, rate limiting, token validation
Databases: PostgreSQL, MongoDB with encryption enabled
Cloud Security: AWS IAM, Azure Security Center, Google Cloud IAM
DevSecOps Tools: SonarQube, Snyk, OWASP ZAP
Monitoring: SIEM systems, log management tools
Using modern frameworks with built-in security features improves overall resilience.
Cost Factors in Implementing App Security Best Practices
The cost of secure app development depends on several elements:
Application complexity and data sensitivity
Compliance requirements (HIPAA, PCI-DSS, GDPR)
Multi-factor authentication implementation
Encryption standards and infrastructure
Security testing scope (manual vs automated)
Third-party penetration testing
Ongoing monitoring and patch management
While security adds initial investment, it significantly reduces long-term breach recovery costs and regulatory fines.
Latest Trends in App Development Security
Security strategies continue evolving to address modern threats:
Zero Trust Architecture
DevSecOps automation
AI-driven threat detection
Behavioral analytics for anomaly detection
Biometric authentication
Blockchain-based identity management
Runtime application self-protection (RASP)
Secure containerization and Kubernetes hardening
Staying ahead of emerging threats requires continuous adaptation.
Why Choose Us for Secure App Development?
Building secure applications requires expertise across architecture, development, testing, and compliance. We implement comprehensive app development best practices for security tailored to your industry and business model.
Here’s what sets us apart:
Security-First Development Approach – Embedded security across the SDLC.
OWASP-Compliant Coding Standards – Mitigates top vulnerabilities proactively.
Advanced Authentication Systems – Secure token handling and MFA integration.
Comprehensive Security Testing – Static, dynamic, and penetration testing.
DevSecOps Integration – Automated vulnerability scanning in CI/CD pipelines.
Cloud Security Expertise – Secure deployment across AWS, Azure, and GCP.
Continuous Monitoring & Incident Response – Rapid mitigation and patching strategies.
We don’t just develop apps — we engineer secure digital ecosystems that protect your users and your business.
Ready to secure your application from day one?
Let’s implement industry-leading app security best practices tailored to your platform.
Contact us today for a comprehensive security assessment and consultation.
Key Points :
- Comprehensive app security strategy covering architecture, authentication, APIs, data storage, and network protection.
- Security-first development approach integrated across the entire Software Development Lifecycle (SDLC).
- Strong authentication & authorization practices including MFA, OAuth 2.0, JWT, and role-based access control (RBAC).
- OWASP Top 10 compliance to mitigate common vulnerabilities like injection attacks and broken authentication.
- Secure API development best practices with token validation, rate limiting, and input/output validation.
- Automated security testing & DevSecOps integration for continuous vulnerability detection in CI/CD pipelines.
FAQ's
The app development best practices for security include secure coding standards, encryption, authentication, API protection, testing, and continuous monitoring integrated throughout the SDLC.
Encryption protects sensitive data during transmission and storage, preventing unauthorized access.
It’s a globally recognized list of the most critical web and mobile application security risks.
DevSecOps integrates automated security testing into CI/CD pipelines to detect vulnerabilities early.
It involves authentication tokens, rate limiting, input validation, and encrypted communication to prevent abuse.
Dependencies should be reviewed and updated regularly to patch known vulnerabilities.
GDPR, HIPAA, PCI-DSS, and ISO 27001 commonly influence application security requirements.
Yes. We offer ongoing vulnerability scanning, monitoring, patch management, and incident response support to ensure continuous protection.